Mobile device management has become even more important now that more people today use personal mobile devices like smartphones and tablets for business purposes. Such devices, coupled with greater Wi-Fi accessibility and cloud services, have empowered us with the ability to access data and do business from practically anywhere at anytime.
Needless to say, many small-to-medium sized business owners have embraced the BYOD (Bring-Your-Own-Device) revolution. The benefits are obvious; increased employee productivity, enhanced services to customers/clients, and better overall customer and employee satisfaction.
But what about the potential consequences associated with this mobility revolution? Are small business owners doing enough preemptive planning to address potential risks that could arise with the use of BYOD devices? Are they using mobile device management to help secure the devices and their IT infrastructure?
What is BYOD?
BYOD (bring your own device) in IT terms, refers to a policy that allows employees use personal devices to connect to companies network, access business applications, and company data. Personal devices may include smartphones, tablets, or personal computers.
An estimated 59% of businesses have a BYOD policy in place and this number is increasing every year.
What is Mobile Device Management?
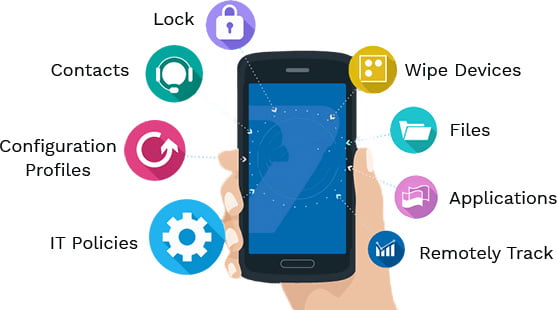
Mobile Device Management (MDM) is a type of security software used by IT departments to monitor, manage, and secure employees’ mobile devices—such as smartphones, tablets, and laptops that are deployed across multiple mobile service providers and across multiple mobile operating systems being used in the organization.
It can be used to monitor hardware, remotely wipe devices that have been lost, and ensuring security standards are met before allowing the device access to sensitive company data to name just a few uses. Think of it like a digital toolbox for companies to keep all their employees’ smartphones, tablets, and laptops safe, up-to-date, and working correctly.
What are some of the Features of Mobile Device Management?
- Device Configuration Management: Allows administrators to configure settings and policies on mobile devices, such as Wi-Fi settings, email accounts, and VPN configurations.
- Application Management: Enables the installation, updating, and removal of apps on mobile devices. This can include managing enterprise apps and ensuring that only approved apps are installed.
- Security Management: Provides security features such as enforcing password policies, encrypting data, remotely locking or wiping devices, and managing compliance with security policies.
- Device Tracking and Inventory: Helps in tracking the location of devices, keeping an inventory of devices, and ensuring that all devices are accounted for.
- Content Management: Manages access to corporate content on mobile devices, ensuring that sensitive data is properly secured and accessible only to authorized users.
- Compliance and Monitoring: Monitors devices to ensure they comply with organizational policies and provides reports and alerts for non-compliance or potential security threats.
- Support and Troubleshooting: Offers tools for remote troubleshooting and support, helping IT departments address issues on mobile devices without needing physical access to them.

Mobile Device Management – Questions Every SMB Should Ask
First, it is important that small business owners honestly assess whether their systems, networks, data, and overall infrastructure are ready for the use of an array of mobile devices.
Once it is firmly established that both internal IT and components in the cloud are prepared for BYOD, solutions should then be put into practice that are concurrent with terms of use policies or any guidelines pertaining to remote and/or telecommute workers or the sharing of sensitive data. The following questions should be answered.
- What particular devices or applications are permissible for work use? Assuming security requirements are in place, not every device or application will meet those.
- Will anyone in the company be tasked with the daily management of BYOB strategies? What should BYOD policies cover and what kind of management solutions will be needed? Would a mobile device management tool that collects device information, deploys and monitors usage, and offers insight into compliance be helpful?
- Which costs will be the responsibility of the employee? This pertains to any fees associated with usage – from network plans to the device itself to software, accessories, and maintenance costs.
- What data will be accessible? Will data encryption be necessary for certain information traveling through the personal devices of employees? Which employees will have read, write, update/delete privileges?
- What is the process when handling sensitive data stored on lost or stolen devices, or the personal devices of ex-employees? Does the company or organization have the right to wipe out the entire device or just corporate data and apps?
Mobile Device Management Conclusion
BYOD is here to stay as it affords smaller-sized companies the mobility of a corporate giant without a huge investment. But when it comes to ensuring that devices, applications, and networks are safe from the variety of threats linked to greater mobility, small business owners may find it necessary to enlist the help of a managed service provider to adequately take on and implement mobile device management for their networks and the challenges that arise with it.
MDM solutions are essential for organizations that support BYOD (Bring Your Own Device) policies, as well as for those that provide company-owned devices to employees. By centralizing the management of mobile devices, organizations can ensure better security, compliance, and productivity while reducing the risks associated with mobile device usage.
If you need assistance implementing BYOD or mobile device management for your business, contact Pennyrile Technologies today.