4 Things to Consider Before Jumping Into BYOD
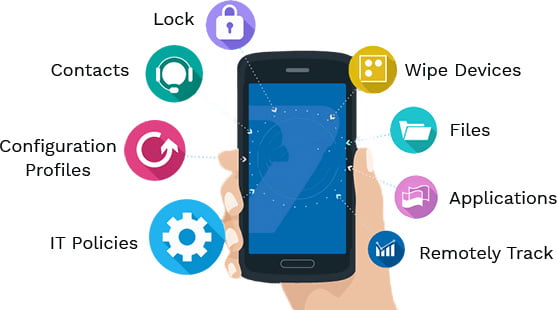
You’ve read it time and time again. “Bring Your Own Device” isn’t a trend, it’s the future. Workplaces, where companies let workers use their own devices for work purposes, are the new normal. What Is Bring Your Own Device BYOD Bring Your Own Device (BYOD) refers to the idea that employees should be allowed to use their personal devices to access company information. The main advantage of this approach is that it makes sure that the employee will always have his/her data available, even when he/she isn’t using the office computer. There are a few reasons why companies are beginning to allow this type of policy. First, many workers are already bringing their own laptops and smartphones to work. If employers don’t want them to do so, then they could simply ban these items from being brought into the workplace. Another benefit is that BYOD allows businesses to save money. Employees who bring their own technology usually won’t need IT support, and they’ll also avoid buying equipment for the business. However, there are some drawbacks to allowing this kind of policy. For example, it can make the job of the security team more difficult. This is because people may be accessing sensitive data that the employer would like to keep private. BYOD attracts new hires and lifts employee morale and productivity. But this doesn’t mean a small business owner should recklessly jump right into BYOD just because everyone else is doing it. There are a few drawbacks to bringing your phone into the office which you need to be aware of. BYOD Security The first issue relates to security. If you’re not careful then you could end up putting your entire business at risk. Data and network security concerns have to be thought out, defined, and addressed in a comprehensive BYOD policy. You need to make sure you take the time to educate your employees about it. When talking about IT security, employees are often the weakest link in a company. It’s important they know what they can and cannot do on their personal devices, why it matters, and what happens if the policy is broken. By implementing a BYOD policy, you can help protect against data breaches and cybersecurity threats. BYOD Cost of Support Most businesses salivate at the thought of the money saved by having employees participate in a BYOD program. With employees using their own devices for work, there is no need to shell out thousands of dollars for desktop PCs, smartphones, tablets, and laptops. While that’s undoubtedly a huge incentive, extra support costs must also be factored in. Chances are your employees aren’t necessarily tech savvy and will need help deploying applications and performing basic yet very necessary maintenance techniques. Unless you have a dedicated IT support team, which most SMBs do not have, you will need to turn to a Managed Service Provider (MSP) in your region for support. A MSP can provide specialized expertise and leverage Mobile Device Management (MDM) tools to keep your network infrastructure and business applications monitored, secured and fully optimized. Limited Number of Support Devices Obviously, you can’t accommodate EVERY employee-owned device. Limiting the types of devices accepted in your BYOD program will mitigate any need to pay for software or equipment upgrades for outdated devices and keep your infrastructure safer as a whole. It’s important to not be too exclusive, select a broad range of devices and their more recent releases to accommodate the varied preferences/tastes of your employees. BYOD Legal Risks Adopting BYOD at your workplaces will expose your company to more legal risks. Sensitive business or private client/customer data can potentially be exposed if devices are lost or stolen. The personal online habits of your employees can also increase your network’s vulnerability to viruses, phishing, or hacking schemes designed to steal such data. These increased legal risks are another reason why SMBs must take precautions such as working with an MSP that offers a solid MDM solution to ensure all employee devices are configured, deployed, managed and monitored in a manner that prioritizes data integrity and security. Ready to implement BYOD for your business? Contact us today for a free evaluation and see how Pennyrile Technologies can help your business today.
4 Things to Consider Before Jumping Into BYOD Read More »